It’s more important than ever to accurately assess underappreciated risk and threat vectors and to identify effective and efficient ways to address them.
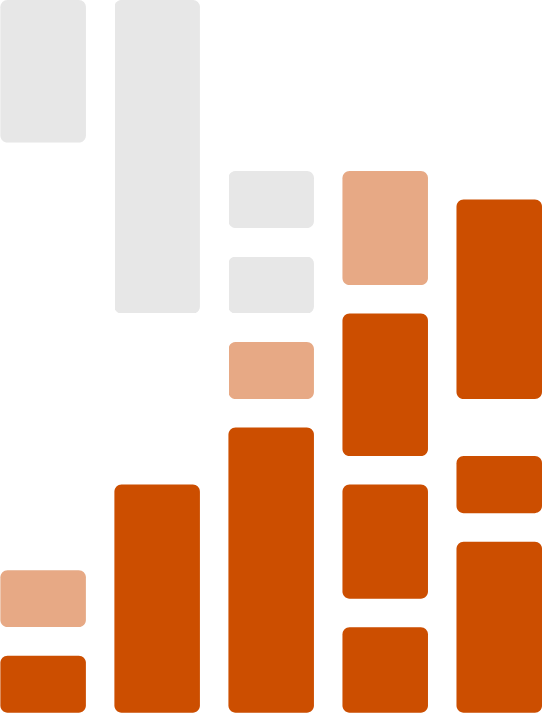
Our latest research shows the average number of planned investments in Cybersecurity technology tops all other tech categories we studied.
We work closely with vendors and end users alike to stay up to date on how organizations are investing, what problems they’re trying to solve, and how the market is changing or adapting to the latest trends. Enterprise Strategy Group’s Cybersecurity analysts and research cover every aspect of an organization’s cybersecurity needs and lifecycle, including:
- Application security
- Cloud security
- Cyber risk management
- Data security
- Identity & access management
- Network security
- Security operations
- Threat detection & response
- User protection
Research Report
Security Hygiene and Posture Management Remains Decentralized and Complex
Security hygiene and posture management has become increasingly difficult because of factors like a growing attack surface, the increased use of cloud computing, and the need to support a remote workforce. These factors can create security vulnerabilities that lead directly to cyber-attacks.
Analysts Covering Cybersecurity

John Grady
Principal Analyst, Network Security & Web Application Security
Areas of Expertise
- Bot Mitigation
- CASB
- DDoS
- Firewall
- IPS
- Microsegmentation

Dave Gruber
Principal Analyst, Ransomware, SecOps & Services
Areas of Expertise
- Data Leakage Prevention
- DevSecOps
- Extended Detection & Response
- Managed Detection & Response
- Ransomware Security Strategies
- Security Analytics

Gabe Knuth
Senior Analyst, End-user Computing & User Protection
Areas of Expertise
- Desktop & App Virtualization (VDI)
- Desktop-as-a-Service (DaaS)
- Digital Employee Experience (DEX)
- Digital Workspaces
- Email Security
- End-User Devices & Hardware

Melinda Marks
Practice Director, Application & Cloud Security
Areas of Expertise
- API Security
- Application Security
- Cloud Security Posture Management
- Cloud Workload Protection Platforms
- Cloud-native Technologies
- Container Security

Brian McKenna
Senior Analyst, Business Applications & EMEA Analyst Services Director
Areas of Expertise
- Business & Technology Strategy
- Business Applications
- Business Intelligence
- Contact Center
- Customer Data Platforms (CDP)
- Customer Experience/CRM

Aaron Tan
Regional Director, Analyst Services, APAC
Areas of Expertise
- Application Modernization & DevOps
- Business Applications
- Cloud Computing
- Cybersecurity
- DevOps
- IaaS/Cloud

Todd Thiemann
Senior Analyst, IAM & Data Security
Areas of Expertise
- Biometrics and Behavioral Analytics
- Data Protection
- Encryption & Key Management
- Identity & Access Management (IAM)
- Identity Threat Detection & Response
- Leveraging AI and ML to improve cybersecurity

David Vance
Senior Analyst, Risk & Vulnerability Management
Areas of Expertise
- API Security
- Application Security Posture Management
- Application Security Testing
- Attack Surface Management (ASM)
- Cloud Native Application Protection Platforms
- Container Security
Recent Cybersecurity Insights
Infographic | April 24, 2024
Operationalizing Encryption and Key Management
Infographic | April 24, 2024
Generative AI for Cybersecurity: An Optimistic but Uncertain Future
Survey Results | April 19, 2024
The Growing Complexity of Securing the Software Supply Chain
Research Report | April 15, 2024